Context
Many times you many want to automate resource management (provisioning, deploying, deleting, modifying) within Microsoft Azure. There are multiple ways to achieve this. For example using Azure Resource Manager templates, PowerShell scripts, Terraform scripts and many more. However, REST APIs is still favorite for many. These APIs help writing custom applications or integrate this process within existing application. In this blog post, let’s understand how we can call these APIs from Postman. In this manner, we will also understand how to call these APIs from other languages.
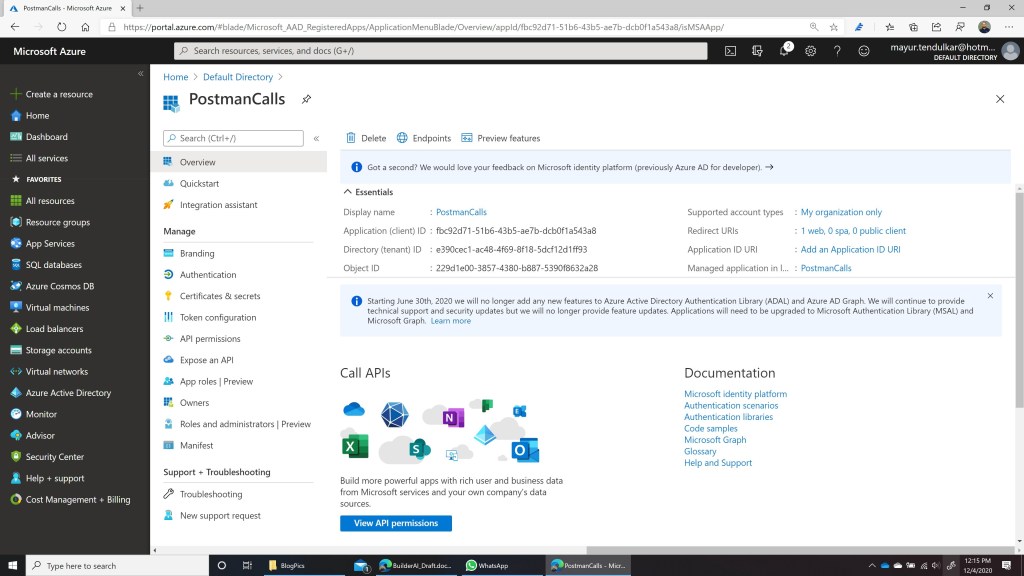
Application Registration
First, navigate to Azure Portal and under Active Directory register a new application. Let’s call it as ‘PostmanCalls‘. Once the app is registered, make a note of Client ID, Tenant ID as it will be required in next steps.
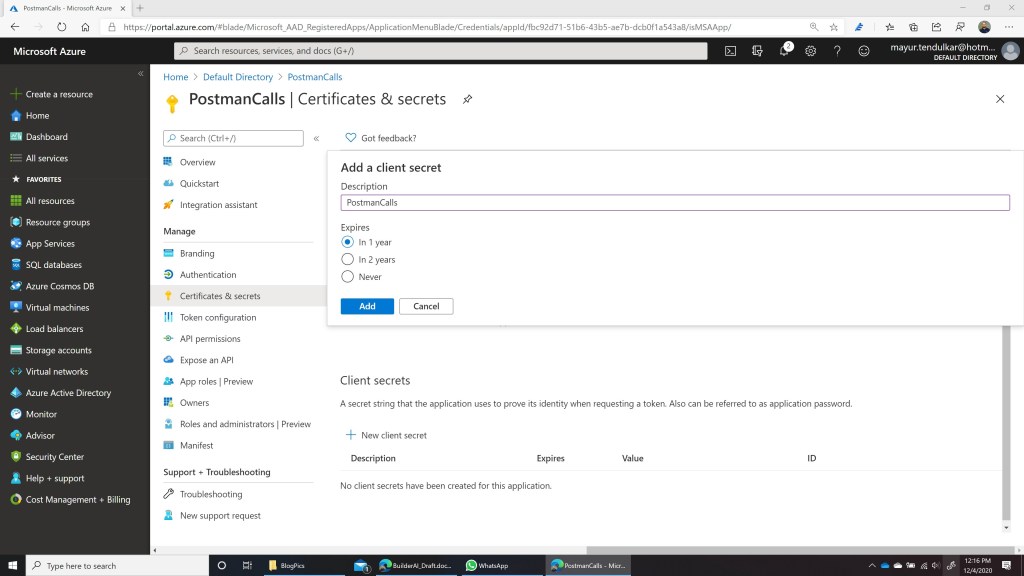
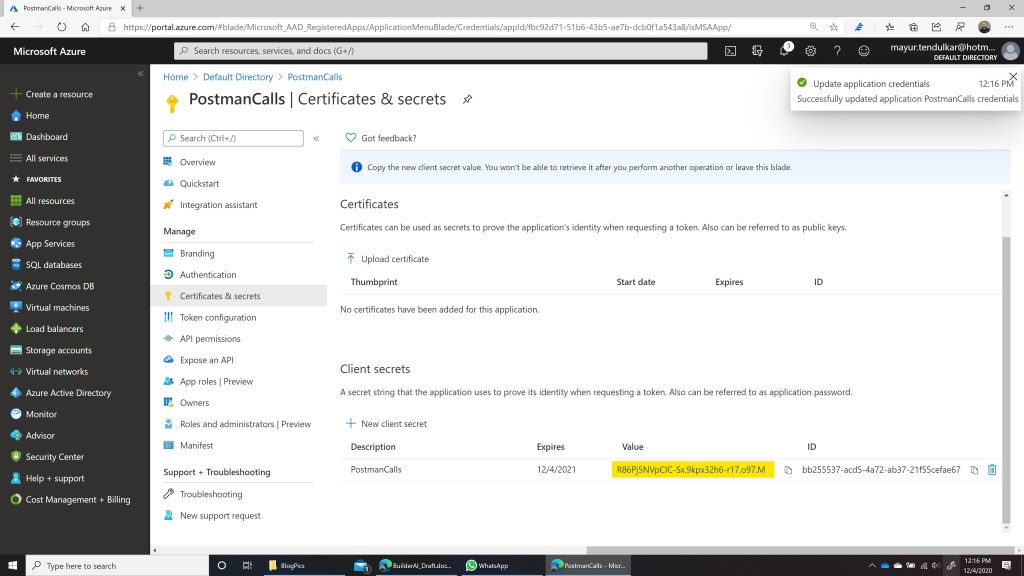
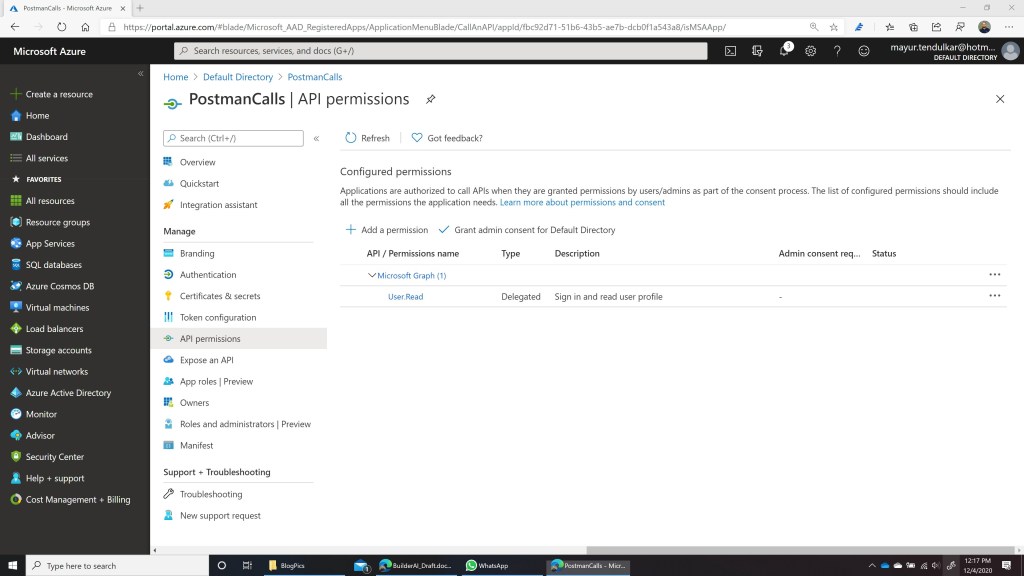
Client Secret and API Permissions
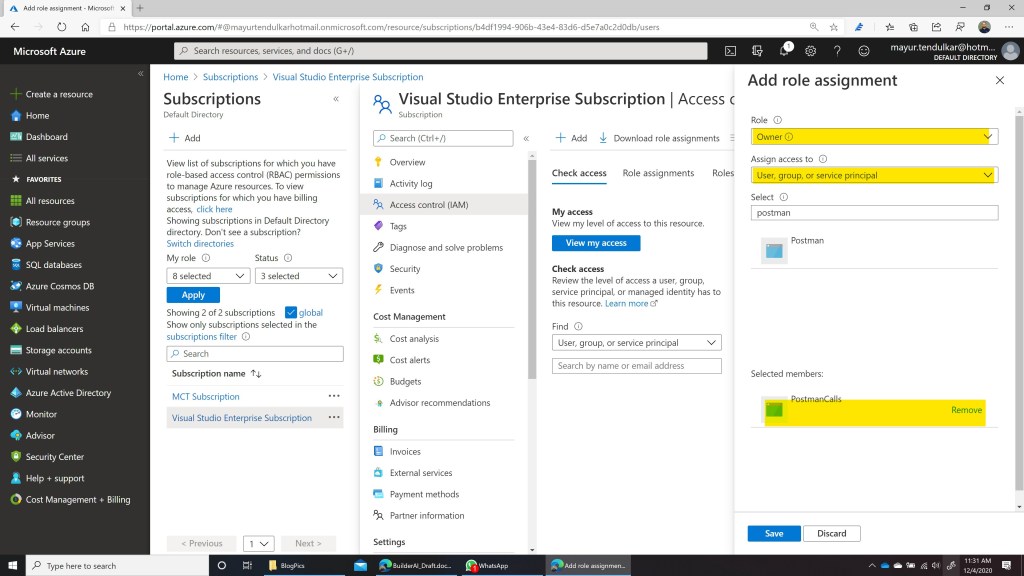
To call the APIs from Postman, let’s create Client Secret and provide permissions to Azure API from this newly registered application. Also grant admin consent for default directory on the same screen.
Application Permissions
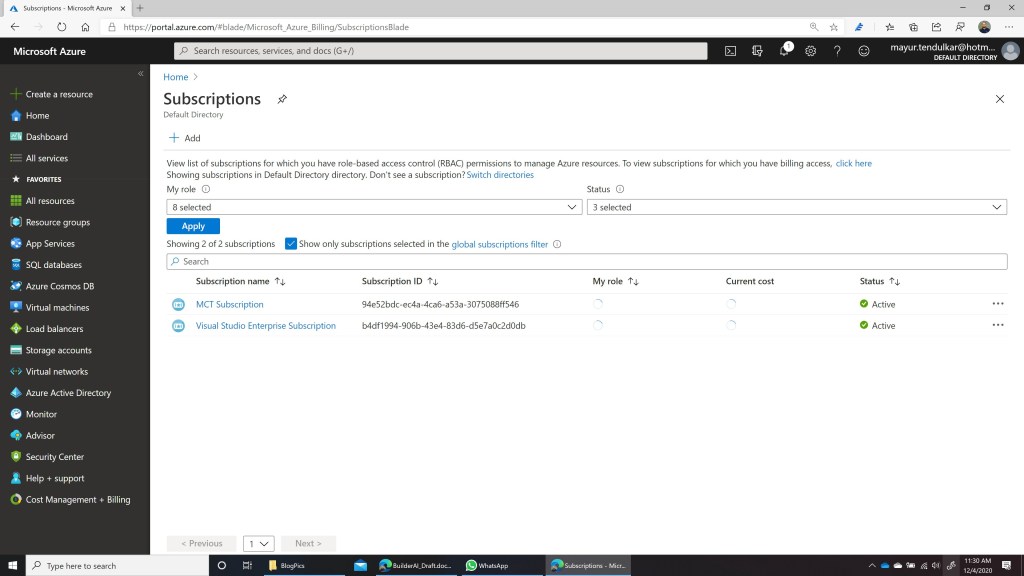
Once the app is registered, let’s give app the permission to modify resources within subscription. In this case I’m providing ‘Owner‘ role which is a God Mode here with full access to ‘PostmanCalls’ app which we have registered sometime back. To do this, go to Subscriptions and provide access to this app.
Acquire Token using Postman
Using Postman, we’ll call Azure Active Directory APIs to acquire a token, which can be used further for calling other rest APIs. In this case, we will be using OAuth2 Token endpoint and Client ID, Tenant ID, Client Secret noted from above steps. The URL looks like this:
https://login.microsoftonline.com/<tenant-id>/oauth2/token OR
https://login.microsoftonline.com/<tenant-id>/oauth2/token?grant_type=client_credentials&client_id=<client-id>&client_secret=<client-secret>&resource=https://management.azure.com/

Note the token returned from above request. This will be required in next step.
Call Management API
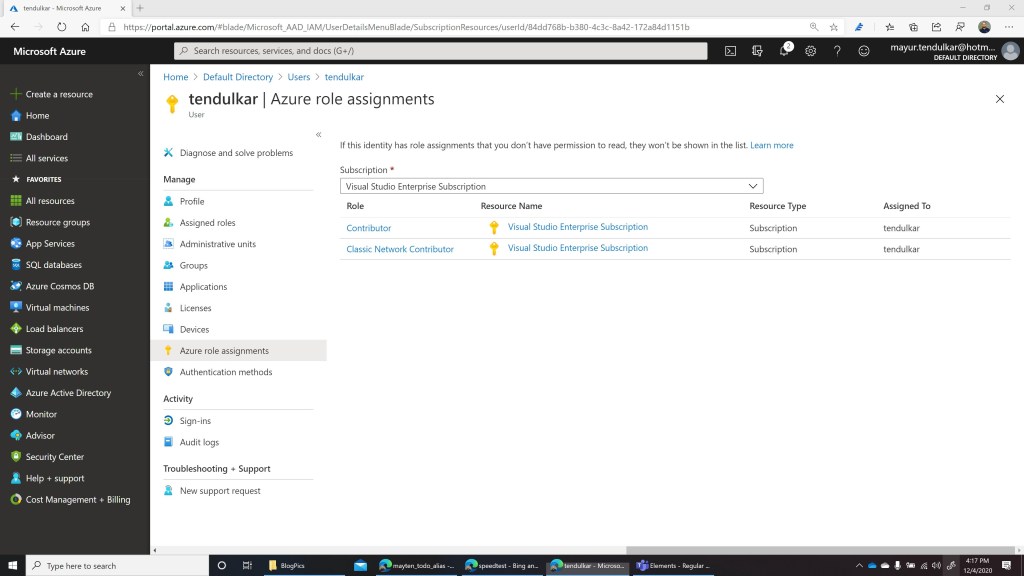
Almost every resource in Azure has API associated with it. You can create Storage Account, Virtual Machine, User, etc using these API. To make it interactive, let’s see how we can assign role to existing user. To understand roles, currently I’ve ‘tendulkar’ user available in my Active Directory and having 2 roles as Contributor and Classic Network Administrator.
To assign roles, we’ve a Azure API documented here. To assign a role to user, we need to call this API as PUT method and provide Object ID (ID of the user) and new Role ID (can be found here for roles). We also need to provide a GUID (generate it using any tool). So the Request becomes:
PUT
https://management.azure.com/subscriptions/<subscription id>/providers/Microsoft.Authorization/roleAssignments/<generated-guid>?api-version=2015-07-01
Body:
{
"properties": {
"roleDefinitionId": "/subscriptions/<id>/providers/Microsoft.Authorization/roleDefinitions/<guid from link>",
"principalId": "<user id/object if>"
}
}

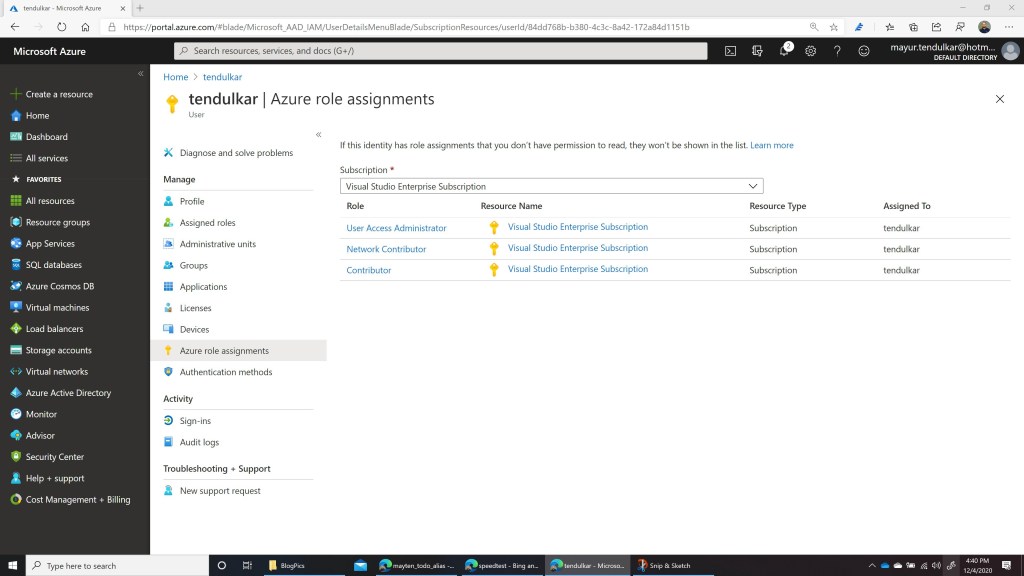
Once the API is called, Role will be assigned to the user and this can be verified from portal. In this case I used ‘Network Contributor’ role to assign.
Conclusion
In this way, we can automate most of the things which can be done through Azure Portal using Azure REST API. We should be able to call these API from any language and any platform which understands HTTP protocol. We just need to register the app with Active Directory, provide right permissions and call right API endpoints.
Happy coding:)
Namaste,
Mayur Tendulkar